Are Excel Macros a Security Risk? A Practical Guide
Explore whether Excel macros pose a security risk, how malware exploits them, and practical steps to secure workbooks, control macro use, and audit VBA projects.
Excel macros security risk is the potential for macro-enabled workbooks to execute VBA code that could compromise data, systems, or privacy. This risk grows when macros come from untrusted sources.
What makes Excel macros risky
According to XLS Library, macros are a powerful way to automate repetitive tasks in Excel, but their ability to execute code also creates a potential security risk. Macros run Visual Basic for Applications (VBA) scripts inside workbooks. If a macro is crafted with harmful code, it can modify data, exfiltrate information, or install unwanted software when the file is opened or macros are enabled. The risk is not inherent to every macro; it depends on provenance, the environment, and how users handle macro-enabled files. In practice, business users often receive macro-enabled templates from external sources, which elevates the chance that a malicious payload could slip past defenses. The key is governance: enforce safe handling, verify publishers, and educate users about potential red flags. The goal of this article is to explain the risk landscape clearly and give you practical steps to maintain automation benefits while reducing exposure.
How macro malware typically spreads
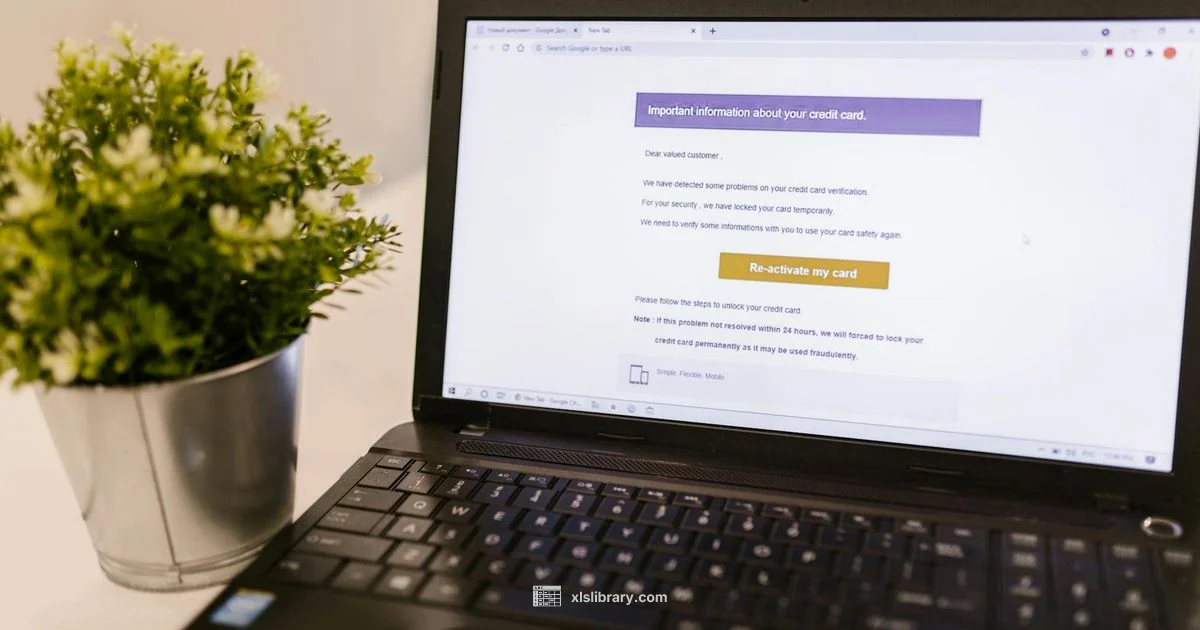
Macro-based attacks commonly reach users through phishing emails that lure them to open an attached workbook with a hidden or visible macro. Attackers also compress macro files in password protected archives to dodge basic scans, or host macro enabled templates on compromised websites. Once enabled, VBA code can run and perform actions such as altering data, harvesting credentials, or downloading additional malware. The attack surface expands when teams share templates across departments, rely on outdated macro libraries, or open files from untrusted sources. Recognizing these patterns is the first defense: verify the source, treat unsolicited attachments with suspicion, and avoid enabling macros in files from unknown origins. According to XLS Library analysis, many macro incidents involve social engineering and insufficient workspace controls, underscoring the need for strong governance alongside technical safeguards.
How to differentiate safe macros from risky ones
Not all macros are dangerous, but safe macros come with hygiene practices. Always verify the macro’s publisher and, if possible, use digitally signed VBA projects. Check the macro’s purpose by reading its code or asking the creator for documentation. In a controlled environment, enable macros only for trusted locations and with macro settings that prompt before execution. Use file extensions as a quick signal, with .xlsm or .xlsb indicating macro support, while .xlsx should be macro free. Enforce least privilege in access to workbook objects and avoid macros that rely on system-wide shortcuts or external scripts. Finally, maintain a clear approval process for new templates and audit trails for changes. A disciplined approach helps you separate practical automation from risky automation.
Best practices for secure macro development
If you must develop macros, follow secure coding guidelines. Start with Option Explicit to reduce variable misuse, and document every function’s purpose. Use early exits and robust error handling to limit unintended side effects. Avoid hard coded paths or credentials, and store sensitive data outside the workbook when possible. Implement digital signatures and keep signing certificates up to date. Establish a formal development–testing–production pipeline, with code reviews and automated tests where feasible. Restrict macro access to necessary spreadsheet ranges and avoid dynamic code construction that could hide harmful logic. Finally, educate users about prompts, permissions, and how to report suspicious behavior. These practices reduce risk without sacrificing the efficiency gains from automation.
Controls and settings in Excel to limit risk
Microsoft Excel provides several layers of defense in Trust Center settings. Disable automatic macro execution and enable prompts, so users decide when code runs. For trusted organizations, use a central macro repository with digital signatures and a controlled distribution process. Enforce workbook and worksheet protection, and consider using password protection for sensitive templates. When possible, implement environment restrictions that block macros from accessing the internet or external drives. Regularly update Office and security patches to close known vulnerabilities. Keep anti-malware software updated and run macro scans as part of routine security hygiene. Taken together, these controls create a layered defense that preserves automation while reducing exposure.
How to audit VBA projects and macro enabled workbooks
Auditing is essential for reducing macro related risk. Start by inventorying macro-enabled files and confirming which workbooks contain VBA projects. Review the code for dangerous patterns such as dynamic code generation, file I O operations, or external connections. Check for digital signatures on the VBA project and verify certificate validity. Use built in Office tools or third party analyzers to scan for known risky constructs. Maintain an evidence trail of changes and approvals. When in doubt, isolate suspicious workbooks in a sandbox before opening in production. Regular audits identify drift between approved templates and what users actually run, making it easier to intervene early.
Alternatives to macros for automation
If you want to reduce macro risk, consider alternatives that achieve similar outcomes with lower risk. Power Query and Power Automate can automate data workflows without embedding VBA in documents. Excel formulas and dynamic array functions can handle many calculations without running code. Shared data models and pivot tables provide automation friendly reporting, while centralizing logic in an add on or external automation service avoids distributing code in workbook files. When automation is necessary, keep macros small, well documented, and limited to confined workbooks rather than global templates. These approaches preserve productivity while decreasing exposure to macro based threats.
Common myths and misconceptions about macros
Myth: macros are inherently dangerous and should never be used. Reality: macros are powerful tools that carry risk only when provenance, governance, and execution controls are weak. Myth: enabling macros is always a security risk. Reality: enabled macros from trusted sources with digital signatures in a controlled environment can be safe. Myth: macro security is just about antivirus. Reality: macro security involves people, processes, and technology, including secure development practices, access controls, and regular audits. Myth: once a macro is created, it cannot be updated safely. Reality: with proper version control and signing, macros can be maintained securely. By recognizing the myths, you can focus on the governance and tooling that enables safe automation rather than avoiding automation entirely.
People Also Ask
What is a macro in Excel?
A macro is a recorded sequence of Excel actions saved as VBA code to automate repetitive tasks. Macros can save time, but they also carry potential security risks if the code is malicious or from an untrusted source.
A macro is a saved sequence of actions in Excel that runs VBA code to automate tasks, but it can be risky if the source isn’t trusted.
Why are macros considered risky in Excel?
Macros can execute code that accesses files, networks, or system resources. When created by attackers or obtained from untrusted sources, they can install malware, steal data, or alter workbook content.
Because macros run code, they can be used to spread malware if the source isn’t trusted.
How can I tell if a workbook has macros?
Look for files with .xlsm or .xlsb extensions and enable macro alerts in Excel. You can also inspect the Developer tab to review the VBA project and see what code is present.
Check the file extension and enable macro alerts to see whether a workbook contains macros.
What are best practices to secure macros?
Use digital signatures on macros, keep software updated, disable auto execution, enable prompts, limit macro execution to trusted locations, and educate users on recognizing suspicious activity.
Sign macros, keep systems updated, and require prompts before running them.
Can macros be used safely in a business environment?
Yes, with strong governance: approved templates, signing, controlled distribution, user training, and regular auditing. Centralize automation where possible to minimize distribution of code in files.
Yes, safely with good governance and controlled deployment.
The Essentials
- Govern macro use before enabling automation.
- Disable automatic execution and require prompts.
- Sign macros digitally and verify publishers.
- Audit macro-enabled files regularly.
- Explore safer automation alternatives when possible.